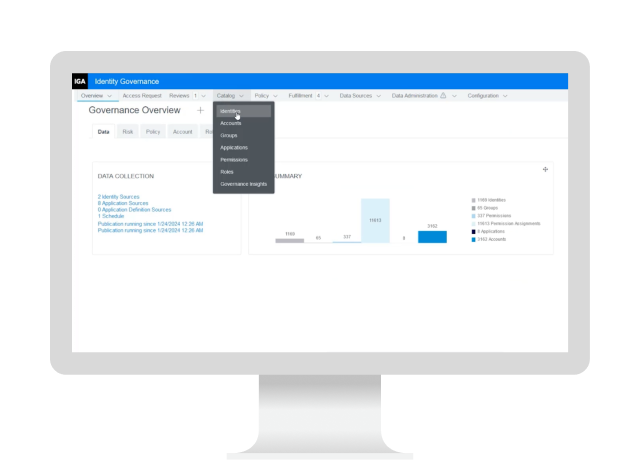
OpenText Identity Governance (NetIQ)
Protect data with simplified compliance and access review processes
KuppingerCole IGA Leadership Compass reportRead the report
Overview
Managing access to sensitive data across an organization is complex and time-consuming, often leading to security risks and compliance challenges. Ensuring the right users have the right access—while minimizing manual oversight—is critical.

OpenText™ Identity Governance (NetIQ) offers a precise and efficient solution for managing user access. By automating reviews, approvals, and policy enforcement, it ensures only authorized users access critical resources, reducing security risks and human error. It simplifies compliance with regulatory standards and provides real-time visibility into access, helping IT teams swiftly address risks, cut down manual processes, and reduce costs.
Why OpenText Identity Governance?
Real-time identity and access management provides constant, consistent reconciliation, which is essential for risk management and attestation.
- Unified
comprehensive platform
Governs access to all resources across your environment, whether deployed on-premises or via SaaS. - Automated
continuous compliance monitoring
Automates access certification processes and adjusts security controls in real-time, ensuring continuous compliance and reducing organizational risk. - Billions
of identities can be managed via scaling
Manages billions of identities, streamlining access requests, certifications, and lifecycle management for large enterprises.
Use cases
Ensuring the right users have the right access—while minimizing manual oversight—is critical. By automating reviews, approvals, and policy enforcement, only authorized users access critical resources, reducing security risks and human error.
-
Align access permissions continuously with regulatory requirements via automated access reviews and policy-driven governance. Automation reduces manual effort for tracking compliance so IT teams can quickly generate accurate reports and demonstrate adherence to industry standards.
-
Mitigate security risks with deep visibility into access permissions and their justifications. The solution leverages intelligent algorithms to detect and address anomalies or unauthorized access, reducing the likelihood of data breaches.
-
Reduce time spent on manual data collection and analysis with automated record-keeping and policy enforcement that ensure all necessary audit trails are readily available.
-
Eliminate manual processes and streamline access control workflows to enable faster response times to access requests and reduce the risk of delays. This increased efficiency improves operational effectiveness and supports a more agile and responsive IT environment.
Key features
Overhaul how identities are continually managed with access governance, entitlement collection, approval management and analytics.

Access governance
Governs access to all resources across your environment, whether you choose to deploy on premises or via SaaS.

Entitlement collection
Collects and visualizes identities and entitlements across your entire environment.

Approval management
Automates application fulfillment with a user-friendly, self-service access request and approval system.

Analytics access
Reduces rubber stamping with analytics that provide business context and risks associated with each request.

Continuous governance
Triggers access reviews on high-risk changes, with interventions needed only for exceptions.
Accelerate the value of OpenText Identity Governance
Services
Accelerate digital transformation with guidance from certified experts.
-
Modernize your information management with certified experts
Professional Services
-
Turn support into your strategic advantage
Support Services
-
Meet business goals with expert guidance, managed services, and more
Customer Success Services
-
Free up your internal teams with expert IT service management
Managed Services
Partners
OpenText helps customers find the right solution, the right support, and the right outcome.
Global system integrators (GSIs)
These GSIs are trained and certified on OpenText solutions, offering services that enhance the value of stand-alone solutions.
Training
OpenText Learning Services offers comprehensive enablement and learning programs to accelerate knowledge and skills.
-
Meet the demands of all types of users for effective adoption
Learning Services
-
Get expertise as needed
Flexible Credits
Communities
Explore our OpenText communities. Connect with individuals and companies to get insight and support. Get involved in the discussion.
-
Explore and vote on ideas, participate in the forums, and network with your peers
OpenText Enterprise Cybersecurity Community
-
Expert insights, threat intel, and product updates—built for SMBs
OpenText Cybersecurity SMB Community
Premium Support
Optimize the value of your OpenText solution with dedicated experts who provide mission-critical support for your complex IT environment.
OpenText Identity Governance resources
OpenText Identity Governance
Read the product overviewOpenText Identity Manager
Read the product overviewOpenText Identity Manager
Read the product overview-
Identity governance and administration (IGA) is a framework that combines identity lifecycle management with access governance. It ensures that the right individuals have access to the right resources at the right times, enhancing security and compliance.
-
IGA is crucial for improving regulatory compliance, reducing security risks, and streamlining user access management. It helps organizations enforce the principle of least privilege, maintain audit trails, and automate provisioning and deprovisioning processes.
-
Continuous risk reduction adapts to changes and events as they happen in real time. It automatically initiates compliance reviews and triggers access reviews on high-risk changes. Interventions are needed only for exceptions, ensuring timely and relevant reviews to maintain compliance.
-
It automates access review and recertification processes, ensuring that access levels are compliant with regulatory standards and reducing the risk of data breaches.
-
By automating administrative tasks and eliminating manual processes, it boosts operational efficiency, reduces errors, and allows information handlers to focus on their primary responsibilities.
-
Risk scoring helps evaluate and prioritize access risks dynamically, improving risk management and ensuring that high-risk changes trigger necessary access reviews.

Not ready for ITDR? You can still go adaptive
ITDR protects against identity-based attacks, but IAM still offers advanced protection.
Read the blog
OpenText recognized as a leader in KuppingerCole’s 2024 IGA Leadership Compass
What do secure systems, smooth audits, and good sleep have in common? Resilient identity governance.
Read the blog