Why OpenText
Why OpenText
Overview Why OpenText
OpenText brings decades of expertise to help you unlock data, connect people and processes, and fuel AI with trust
Manage and connect data
Unify data seamlessly across your enterprise to eliminate silos, improve collaboration, and reduce risks
AI-ready information
Get AI-ready and transform your data into structured, accessible, optimized information
Built-in security and compliance
Meet regulatory and compliance requirements and protect your information throughout its lifecycle
Empowering people
Overview Empowering people
OpenText helps people manage content, automate work, use AI, and collaborate to boost productivity
Customers
See how thousands of companies around the world are succeeding with innovative solutions from OpenText
Employees
Our people are our greatest asset; they are the life of the OpenText brand and values
Corporate Responsibility
Learn how we aspire to advance societal goals and accelerate positive change
Partners
Find a highly skilled OpenText partner with the right solution to enable digital transformation
How we compare
Content Management
Service Management
Deploy anywhere
Overview Deployment options
Explore scalable and flexible deployment options for global organizations of any size
Sovereign cloud
Local control. Global scale. Trusted AI
Private cloud
Your cloud, your control
On-premises
Free up resources, optimize performance and rapidly address issues
Public cloud
Run anywhere and scale globally in the public cloud of your choice
AI leadership
Overview Aviator AI
See information in new ways
OpenText™ Aviator AI
AI that understands your business, your data, and your goals
OpenText™ MyAviator
Say hello to faster decisions. Your secure personal AI assistant is ready to get to work
OpenText™ Business Network Aviator
Gain better insights with generative AI for supply chains
OpenText™ Content Aviator
Power work with AI content management and an intelligent AI content assistant
OpenText™ Cybersecurity Aviator
Improve your security posture with AI cybersecurity and agile threat detection
OpenText™ DevOps Aviator
Enable faster app delivery, development, and automated software testing
OpenText™ Experience Aviator
Elevate customer communications and experiences for customer success
OpenText™ Service Management Aviator
Empower users, service agents, and IT staff to find the answers they need
Aviator AI
Overview Aviator AI
See information in new ways
OpenText™ Aviator AI
AI that understands your business, your data, and your goals
OpenText™ MyAviator
Say hello to faster decisions. Your secure personal AI assistant is ready to get to work
OpenText™ Business Network Aviator
Gain better insights with generative AI for supply chains
OpenText™ Content Aviator
Power work with AI content management and an intelligent AI content assistant
OpenText™ Cybersecurity Aviator
Improve your security posture with AI cybersecurity and agile threat detection
OpenText™ DevOps Aviator
Enable faster app delivery, development, and automated software testing
OpenText™ Experience Aviator
Elevate customer communications and experiences for customer success
OpenText™ Service Management Aviator
Empower users, service agents, and IT staff to find the answers they need
Analytics
Overview Analytics
Predict, act, and win with real-time analytics on a smarter data platform
OpenText™ Aviator Search(AI)
Give users access to the answers they need, faster and easier, with multi-repository AI-based search that lets you contextualize everything from clicks to conversations
Business Network
Overview Business Network
Connect once, reach anything with a secure B2B integration platform
Content
Overview Content
Reimagine knowledge with AI-ready content management solutions
OpenText™ Content Aviator(AI)
Supercharge intelligent workspaces with AI to modernize work
Cybersecurity
Overview Cybersecurity
Integrated cybersecurity solutions for enterprise protection
OpenText Cybersecurity for SMBs & MSPs
Purpose built data protection and security solutions
OpenText™ Cybersecurity Aviator(AI)
Reinvent threat hunting to improve security posture with the power of agile AI
DevOps
Overview DevOps
Ship better software—faster—with AI-driven DevOps automation, testing, and quality
Experience
Overview Experience
Reimagine conversations with unforgettable customer experiences
Observability and Service Management
Overview Observability and Service Management
Get the clarity needed to cut the cost and complexity of IT operations
OpenText™ Service Management Aviator(AI)
Redefine Tier 1 business support functions with self-service capabilities from private generative AI
APIs
Overview APIs
Build custom applications using proven OpenText Information Management technology
OpenText™ API Services
Build it your way with OpenText Cloud APIs that create the real-time information flows that enable custom applications and workflows
Device and Data Protection
Overview Device and Data Protection
Protect what matters, recover when it counts
Unified Endpoint Management Tools
- OpenText™ Endpoint Management
- OpenText™ ZENworks Suite
- OpenText™ ZENworks Service Desk
- OpenText™ ZENworks Configuration Management
- OpenText™ ZENworks Endpoint Security Management
- OpenText™ ZENworks Full Disk Encryption
- OpenText™ ZENworks Endpoint Software Patch Management
- OpenText™ ZENworks Asset Management
Solutions
Trusted Data & AI
Overview Trusted Data & AI
Secure information management meets trusted AI
OpenText AI Data Platform
A unified data framework to elevate data and AI trust
OpenText Aviator Studio
A place where you can build, deploy, and iterate on agents in your data's language
OpenText Discovery
A set of tools to help ingest data and automate metadata tagging to fuel AI
OpenText Data Compliance
A suite of services and APIs that make governance proactive and persistent
OpenText Aviator AI Services
Professional services experts who help you on your AI journey
Information Reimagined
Overview Information Reimagined
Get greater visibility and sharper insights from AI-driven information management. Ready to see how?
Knowledge reimagined
Transform daily work with enterprise content management powered by AI
Service Management reimagined
Cut the cost and complexity of IT service management, AIOps, and observability
Connections reimagined
AI-powered B2B integration for supply chain success
Conversations reimagined
Drive value, growth, and loyalty with connected customer experiences
Engineering reimagined
Agile development and software delivery? It only seems impossible
Security reimagined
Cybersecurity for the Enterprise
Decisions reimagined
Unlock insights with AI data analytics
Artificial Intelligence
Overview Aviator AI
See information in new ways
OpenText™ Aviator AI
AI that understands your business, your data, and your goals
OpenText™ MyAviator
Say hello to faster decisions. Your secure personal AI assistant is ready to get to work
OpenText™ Business Network Aviator
Gain better insights with generative AI for supply chains
OpenText™ Content Aviator
Power work with AI content management and an intelligent AI content assistant
OpenText™ Cybersecurity Aviator
Improve your security posture with AI cybersecurity and agile threat detection
OpenText™ DevOps Aviator
Enable faster app delivery, development, and automated software testing
OpenText™ Experience Aviator
Elevate customer communications and experiences for customer success
OpenText™ Service Management Aviator
Empower users, service agents, and IT staff to find the answers they need
Industry
Overview Industry solutions
Improve efficiency, security, and customer satisfaction with OpenText
Energy and resources
Transform energy and resources operations with cloud, cybersecurity, and AI
Financial services
Boost customer experience, compliance, and efficiency with AI
Government
Reimagine your mission with government-secure information management
Healthcare and life sciences
Improve care delivery and patient engagement with AI-powered solutions
Legal
Modernize legal teams with automated, AI-powered legal tech solutions
Manufacturing
Modernize manufacturing operations and logistics to reduce costs and ensure compliance
Retail and consumer goods
Enhance consumer engagement with omnichannel retail solutions and AI
Enterprise Application
Overview Solutions for Enterprise Applications
Run processes faster and with less risk
Services
Services
Overview Services
Achieve digital transformation with guidance from certified experts
Professional Services
Modernize your information management with certified experts
Customer Success Services
Meet business goals with expert guidance, managed services, and more
Support Services
Turn support into your strategic advantage
Managed Services
Free up your internal teams with expert IT service management
Learning Services
Discover training options to help users of all skill levels effectively adopt and use OpenText products
Professional Services
Overview Professional Services
Modernize your information management with certified experts
Customer Success Services
Overview Customer Success Services
Meet business goals with expert guidance, managed services, and more
Support Services
Overview Support Services
Turn support into your strategic advantage
Managed Services
Overview Managed Services
Free up your internal teams with expert IT service management
Learning Services
Overview Learning Services
Discover training options to help users of all skill levels effectively adopt and use OpenText products
Partners
Find a Partner
Overview Find a partner
Information is the heartbeat of every organization. We build information management software so you can build the future
Cloud Partners
Overview Cloud Partners
OpenText partners with leading cloud infrastructure providers to offer the flexibility to run OpenText solutions anywhere
Enterprise Application Partners
Overview Enterprise Application Partners
OpenText partners with top enterprise app providers to unlock unstructured content for better business insights
Partner Solutions
Overview Partner Solutions
Discover flexible and innovative offerings designed to add value to OpenText solutions
Resources for Partners
Overview Resources for Partners
Discover the resources available to support and grow Partner capabilities
Support
Overview Customer Support
Get expert product and service support to accelerate issue resolution and keep business flows running efficiently
Resources
Overview Resources
Explore detailed services and consulting presentations, briefs, documentation and other resources
Choose your region:
Europe, Middle East and Africa
Asia–Pacific
What is digital forensics?

Understanding Digital Forensics

Digital forensics
Why digital forensics matters
In today’s digital world, nearly every crime or cyberattack leaves behind a digital footprint. According to Microsoft, nearly 90% of all crimes include digital evidence. Digital forensics, which includes computer forensics and mobile forensics, provides the tools and methodologies needed to trace that digital footprint, helping digital forensic investigators and examiners uncover the truth, and ensure that evidence is admissible in court and can be trusted by internal stakeholders, regulators, and legal teams. Digital forensics provides the evidence and clarity needed to make informed decisions and is essential for protecting sensitive information, preserving business continuity, and holding malicious actors accountable.
According to Grand View Research, the digital forensics market is expected to grow to $26.1 billion by 2030. This growth is fueled by rising cybercrime investigations, regulatory demands, insider threats, and the increasing use of digital devices in both personal and enterprise settings.
Who uses digital forensics and why?
Digital forensic examiners or investigators use digital forensics tools to analyze digital evidence from various sources, including computers, mobile devices, networks, and cloud sources. The “DFPulse: The 2024 Digital Forensic Practitioner Survey” indicates that the primary users of digital forensics are law enforcement, government agencies, corporate security teams, and forensic service providers.
Law enforcement agencies: Typically use digital forensics tools to collect, analyze, and preserve electronic evidence during investigations. Typical criminal acts investigated include cases involving cybercrime, fraud, theft, violent crimes, and exploitation. Faced with the challenges of obtaining information from locked devices, investigating diverse data sources, conducting comprehensive data extraction, reconstructing digital activity, and maintaining chain of custody, law enforcement professionals look to digital forensics to ensure thorough investigations, close cases faster, and meet evidentiary standards.
Corporations and businesses: Enterprises use digital forensics solutions to protect intellectual property, investigate data breaches and insider threats, investigate employee misconduct and HR violations, and respond to cybersecurity incidents. Digital forensics enables organizations to collect tamper-proof evidence, understand the scope of incidents, and make data-driven decisions while minimizing risk and reputational damage. It's a key pillar of enterprise cybersecurity and governance.
Government and public sector: Government agencies use digital forensics for national security, public safety, and to investigate threats such as terrorism or organized crime. These tools help gather intelligence and ensure the integrity of digital evidence in legal proceedings, enabling decisive action in high-stakes environments ranging from national defense to local government accountability.
Consulting and cybersecurity firms: These organizations provide digital forensics as a service to clients, assisting with incident response, threat analysis, and evidence collection. They help organizations recover from cyberattacks and strengthen their security posture.
Legal firms and courts: Lawyers and legal professionals use digital forensics to collect, preserve, and analyze digital evidence for civil and criminal cases. This evidence can be pivotal in proving guilt or innocence and in supporting legal arguments.
How does digital forensics uncover the truth
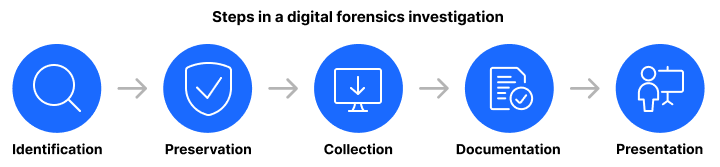
Taking the appropriate steps in a digital forensics investigation is critical because it ensures the integrity, admissibility, and reliability of the evidence:
- Identification: Without knowing where to look, critical data could be overlooked or lost. Early identification shapes the scope and success of the investigation.
- Preservation: Preserving evidence in its original state is essential for maintaining chain of custody and legal admissibility.
- Collection: This step must be performed methodically to avoid contamination, data loss, or introducing bias. It lays the foundation for reliable analysis.
- Examination/analysis: Analysis reveals the who, what, when, where, and how behind the incident. This step provides the investigative insights needed for remediation, legal action, or compliance.
- Documentation/reporting: Clear documentation ensures transparency, supports legal proceedings, and allows results to be reviewed by internal teams, regulators, or in court.
- Presentation/testimony (if required): Communicating technical evidence in a clear, defensible way ensures it holds up under scrutiny and contributes to just outcomes.
Together, these steps ensure that digital investigations are accurate, defensible, and actionable, whether in a courtroom, boardroom, or security operations center (SOC).
Digital forensics vs. digital forensics and incident response (DFIR)?
Digital forensics focuses on the collection, preservation, analysis, and reporting of digital evidence. It's about understanding what happened on a device or network, whether that’s uncovering deleted files, analyzing user activity, or reconstructing timelines. It is typically used by law enforcement, legal teams and forensic analysts in legal investigations, internal audits, and criminal cases to preserve and analyze evidence.
Digital forensics and incident response (DFIR) includes all the elements of digital forensics but expands to include containment and remediation of threats. It’s often used by SOC teams, CISOs, and incident responders in cybersecurity environments to investigate and respond to breaches, malware, or insider threats, minimizing impact, restoring systems, and understanding attack vectors. Think of DFIR as digital forensics plus action, where you not only uncover what happened, but you also do something about it in the moment.
What to look for in an effective digital forensics tool
When evaluating a digital forensics tool, you should look for features that support accuracy, speed, scalability, and legal defensibility, all while aligning with your investigative environment.
Comprehensive evidence collection is the foundation of a reliable, legally sound, and effective investigation. Acquiring data from endpoints, mobile devices, cloud platforms, removable media, and volatile memory ensures investigators have a complete and accurate picture of the incident or activity being examined.
Artifact parsing and recovery is critical in a digital forensics investigation because it allows investigators to extract meaningful, human-readable data from complex system files and unstructured digital traces.
Timeline and correlation analysis are fundamental to digital forensics investigations because they allow investigators to reconstruct events, identify patterns, and uncover evidence that might otherwise remain hidden in large volumes of digital data.
Memory and volatile data analysis are critical in digital forensics investigations because they provide access to transient, actionable evidence that disappears when a system is powered down. This type of analysis uncovers stealthy threats and real-time activities that traditional disk-based forensics often miss.
Forensic soundness is the foundation of any digital forensics investigation because it ensures that digital evidence remains reliable, trustworthy, and admissible in legal proceedings.
Ease of use and workflow efficiency directly impact the speed, accuracy, cost-effectiveness, and overall success of digital forensics investigations.
Defensible reporting is foundational to the credibility, transparency, and success of digital forensics investigations, ensuring that evidence is reliable, legally defensible, and understandable to all stakeholders.
Integration and compatibility is key to a digital forensics tool because they ensure the tool can work effectively within the broader investigative ecosystem, maximizing efficiency, flexibility, and investigative accuracy. Additionally, the ability to integrate with incident response (DFIR) helps minimize damage and reduce dwell time.
Scalability and performance eliminate bottlenecks and ensure that digital forensics tools remain effective and reliable as investigation demands grow in size, urgency, and complexity.
Why choose OpenText for Digital Forensics
From pioneering the industry’s earliest evidence acquisition methods to powering today’s enterprise-scale investigations, OpenText has played a foundational role in how digital evidence is collected, analyzed, and defended in court. Based on three decades of experience in digital forensics, thousands of agencies, corporations, and forensic professionals rely on OpenText every day because of the depth, scale, and legal-grade reliability that few other platforms can match.
OpenText digital forensics solutions are known for their court-validated imaging and analysis. They offer simple, artifact-based workflows in addition to providing deep evidence access with bit-level collection, even from damaged or encrypted drives. Because OpenText digital forensics solutions support remote forensic acquisition across large, distributed enterprise networks, digital forensic investigations can scale to thousands of endpoints with forensic-grade acquisition and deep disk-level visibility, not just log-based EDR-style data.
In addition to providing digital forensics software, OpenText delivers a line of digital forensic hardware such as write blockers, forensic imagers, and forensic duplicators designed to acquire forensic images of a suspect’s devices. These hardware tools integrate seamlessly with OpenText digital forensics software in order to provide investigative teams with a full-stack solution that reduces the need to mix vendors for acquisition and analysis.
OpenText digital forensics tools deliver extensive file system and artifact support, supporting a broad array of file systems and file carving capabilities. With the ability to handle legacy and obscure file systems common in criminal or insider threat investigations, OpenText digital forensics remains a strong choice for end-case file systems.
Whether for law enforcement, corporate investigations, or legal cases, OpenText gives professionals the precision, speed, and confidence they need when the stakes are high.
Power your investigation with OpenText
Discover how OpenText’s digital forensics solutions empower investigators to uncover critical evidence quickly, securely, and with full legal defensibility. Whether you’re managing complex enterprise investigations or conducting criminal casework, OpenText combines decades of expertise with cutting-edge technology to deliver reliable, scalable, and trusted forensics tools. Learn more about how OpenText can elevate your investigations and help you stay ahead in today’s evolving digital landscape by visiting.
Resources
-
Digital Discovery
Digital Discovery finds the facts hidden in data with forensic investigation technology US investigative firm relies on OpenText EnCase to analyze the brave new world of data
-
City of Dallas
Texas city government accelerates information discovery with OpenText security solution. City of Dallas transforms digital forensics with OpenText EnCase for efficiency, productivity and time savings
-
Banner Health
Banner Health transforms information discovery and security with OpenText EnCase solutions. Nonprofit healthcare provider employs OpenText EnCase Information Assurance (formerly EnCase eDiscovery) and OpenText EnCase Endpoint Investigator to accelerate eDiscovery processes and data security
-
Southern Alberta Internet Child Exploitation Unit
Alberta Law Enforcement Unit leverages OpenText EnCase to Significantly Improve Case Efficiency. Internet Child Exploitation Unit (ICE) turns to OpenText EnCase Forensic to close cases faster and prosecute more offenders
Related products
OpenText™ Endpoint Investigator
Effectively investigate internal cybercrimes, data breaches, and fraud
OpenText™ Forensic
Close cases quickly with digital forensic investigation results you can trust
OpenText™ Mobile Investigator
Capture, collect, and analyze critical mobile device evidence faster
OpenText™ Forensic Equipment
Acquire digital evidence in a reliable, defensible, and efficient way
OpenText™ Information Assurance
Strengthen data integrity and compliance with precision and confidence
OpenText™ Endpoint Forensics & Response
Investigate, contain, and remediate cyber threats before damage is done





