OpenText Core Threat Detection and Response
在造成损害之前识别难以检测的威胁
内部威胁检测
别再为误报浪费时间——更快揭示关键威胁。利用 AI 驱动的检测功能了解您的环境并识别他人忽略的内部威胁,从而增强您的安全运营中心 (SOC)。

OpenText™ Core Threat Detection and Response 使用获得专利的自学习行为分析技术来检测内部威胁、凭据滥用并规避基于规则工具的细微异常情况。它能持续学习用户和系统间的正常交互,识别指示风险的偏差,而无需手动调整或添加代理。帮助您的 SOC 减少警报疲劳,优先响应并精准检测高级威胁。
为什么选择 OpenText Core Threat Detection and Response?
利用自适应人工智能来现代化安全运营,减少警报疲劳,更快地检测内部威胁,并为您的团队争取更多时间。
- 减少
行为 AI 基线误报
根据每个实体正常行为的偏差,而不是通用规则或签名,来检测威胁。 - 10+
经验证的创新专利,拥有十多年的专利研究成果
基于 10 多项专利的 AI 技术,可进行高级行为检测和内部威胁识别。 - 80%
红队检测成功率(由熟练的威胁猎手执行)
利用上下文丰富的警报提高威胁猎手的准确性,从而发现隐蔽攻击并加快调查速度。
用例
利用人工智能驱动的检测功能,该功能从您的环境中学习,为 SOC 分析师、威胁猎手和安全领导者提供支持。检测内部威胁,减少警报疲劳,揭露传统工具所忽略的高级攻击。
-
通过自学习行为分析识别恶意内部人员、疏忽行为和被攻破的账户。在不依赖预定义规则的情况下,标记异常访问、权限滥用和可疑数据移动。
-
通过基于行为上下文持续优先化风险的自适应人工智能,揭示重要的威胁。让您的 SOC 团队停止追踪虚假警报,专注于真正的威胁。
-
超越原始日志。通过自动呈现的行为威胁指标、风险评分异常和指导调查的通俗语言上下文,为威胁猎人提供先发优势。
-
捕捉那些缓慢移动、隐蔽且伪装的威胁。行为优先检测在高级攻击升级之前发现其早期迹象,即使是那些没有已知特征的攻击。
关键功能
使用自学习行为分析来现代化您的 SOC,优先处理真实威胁,减少噪音,并随着环境的变化进行调整。

行为分析引擎
对用户和实体行为进行持续基线检测以识别异常活动,例如凭据滥用、横向移动和内部威胁,而无需依赖规则或阈值。

无监督机器学习
通过 AI 学习贵组织的“独特常态”,AI 会随着时间自动调整检测,随着用户、角色和风险因素的变化提高精确度。

上下文丰富的警报
提供清晰、按优先级排列的警报,并解释发生的问题及其重要性,以便分析师更快做出响应,而无需过滤噪音。

基于风险的优先级排序
检查行为的严重性、频率和同伴比较,动态评分和排序威胁,引导注意力到真正紧急的事项。

Microsoft 生态系统集成
从 Microsoft Defender for Endpoint 和 Entra ID 获取遥测数据,利用行为分析丰富检测,提升 Microsoft 工具已识别的检测效果。

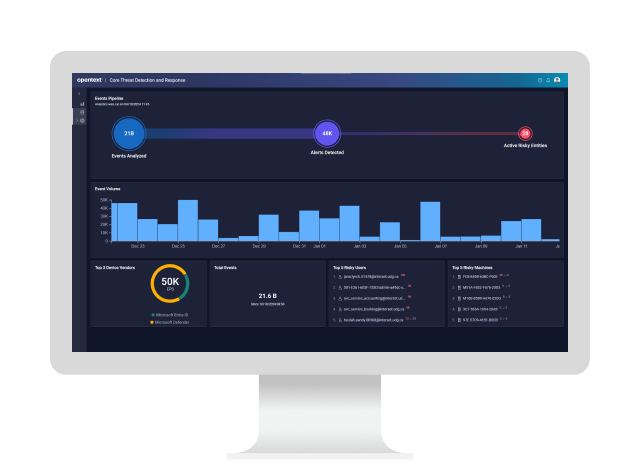
可视化调查仪表板
通过直观的时间线、实体热力图和用户行为趋势,快速分流和调查,从而加快分析师的决策过程。
加速发掘 OpenText™ Core Threat Detection and Response 的价值
集成
扩展您的安全运营能力。
-
通过实时威胁检测和本地 SOAR 将 MTTD 和 MTTR 降到最低
OpenText™ Enterprise Security Manager
-
保护数据、降低风险、提高合规性,并管理访问权限
数据安全
-
通过值得信赖、重新构想的应用程序安全性为开发人员赋能
应用安全测试
-
通过实时网络监控和响应来抵御威胁
OpenText™ Network Detection and Response
-
通过自信地管理身份和访问权限,确保您的数字资产安全
身份和访问管理
合作伙伴
OpenText 帮助客户找到合适的方案、恰当的支持与理想的结果。
全球系统集成商 (GSI)
这些 GSI 均已接受 OpenText 解决方案相关培训和认证,所提供的服务能够提升独立解决方案的价值。
服务
在认证专家的指导下,加速实现数字化转型。
-
通过认证专家实现信息管理现代化
专业服务
-
将支持转化为您的战略优势
支持服务
-
通过专家指导、托管服务等实现业务目标
客户成功服务
-
通过专业的 IT 服务管理解放您的内部团队
托管服务
社区
探索我们的 OpenText 社区。与个人和企业建立联系,获取洞察和支持。参与讨论。
-
浏览创意提案并投票表决,参与论坛讨论,与同行建立社交网络
OpenText Enterprise Cybersecurity Community
-
专家见解、威胁情报和产品更新——专为中小企业打造
OpenText Cybersecurity SMB Community
高级支持
通过专门的专家团队,为您的复杂 IT 环境提供关键任务支持,优化 OpenText 解决方案的价值。
-
获得技术和战略方面的个性化、一对一协助
高级支持
OpenText Core Threat Detection and Response resources
OpenText Core Threat Detection and Response
Read the product overviewThreat detection and response solutions comparison checklist
Learn more5 ways to elevate cyber defense against insider threats
Learn moreBehavioral analytics: Boost your SOC team’s threat detection and response
View the infographicThreat detection and response solutions comparison checklist
Learn more5 ways to elevate cyber defense against insider threats
Learn moreBehavioral analytics: Boost your SOC team’s threat detection and response
View the infographic-
The solution uses unsupervised behavioral analytics to baseline every user and device across Defender for Endpoint and Entra ID telemetry, then flags even slight drift. Peer-group context surfaces malicious, negligent, or compromised insiders early—before privilege abuse or data theft can unfold.
-
Patented ML pipelines build multi-dimensional behavioral baselines for every entity and update continuously. This adaptive AI uncovers zero-day TTPs and low-noise anomalies missed by signatures, rules, or SIEMs, delivering higher-fidelity detections with almost no tuning.
-
SaaS onboarding through native Microsoft APIs is agentless and fast. Point to your tenants, backfill 30 days of history, and actionable detections appear within hours. Full behavioral maturity lands after about two weeks, giving SOCs insight long before traditional rule tuning finishes.
-
Integrated risk scoring suppresses benign anomalies, clusters related indicators, and elevates only high-impact events. The result: up to 90 percent fewer false positives, drastically reduced alert fatigue, and analysts who can focus energy on genuine threats instead of drowning in noise.
-
Online learning refreshes baselines daily, automatically absorbing role changes, shift rotations, mergers, seasonal peaks, and travel patterns. Detection precision remains tight without rule rewrites, keeping insider-threat coverage accurate as the business and its workforce evolve over time.
-
Every alert is tagged with ATT&CK tactic, technique, and step; an LLM-generated narrative links precursor activity to follow-on actions. Analysts know their exact kill-chain position, prior context, and recommended next moves, shortening triage and speeding containment.